Cybersecurity Risk Register Template
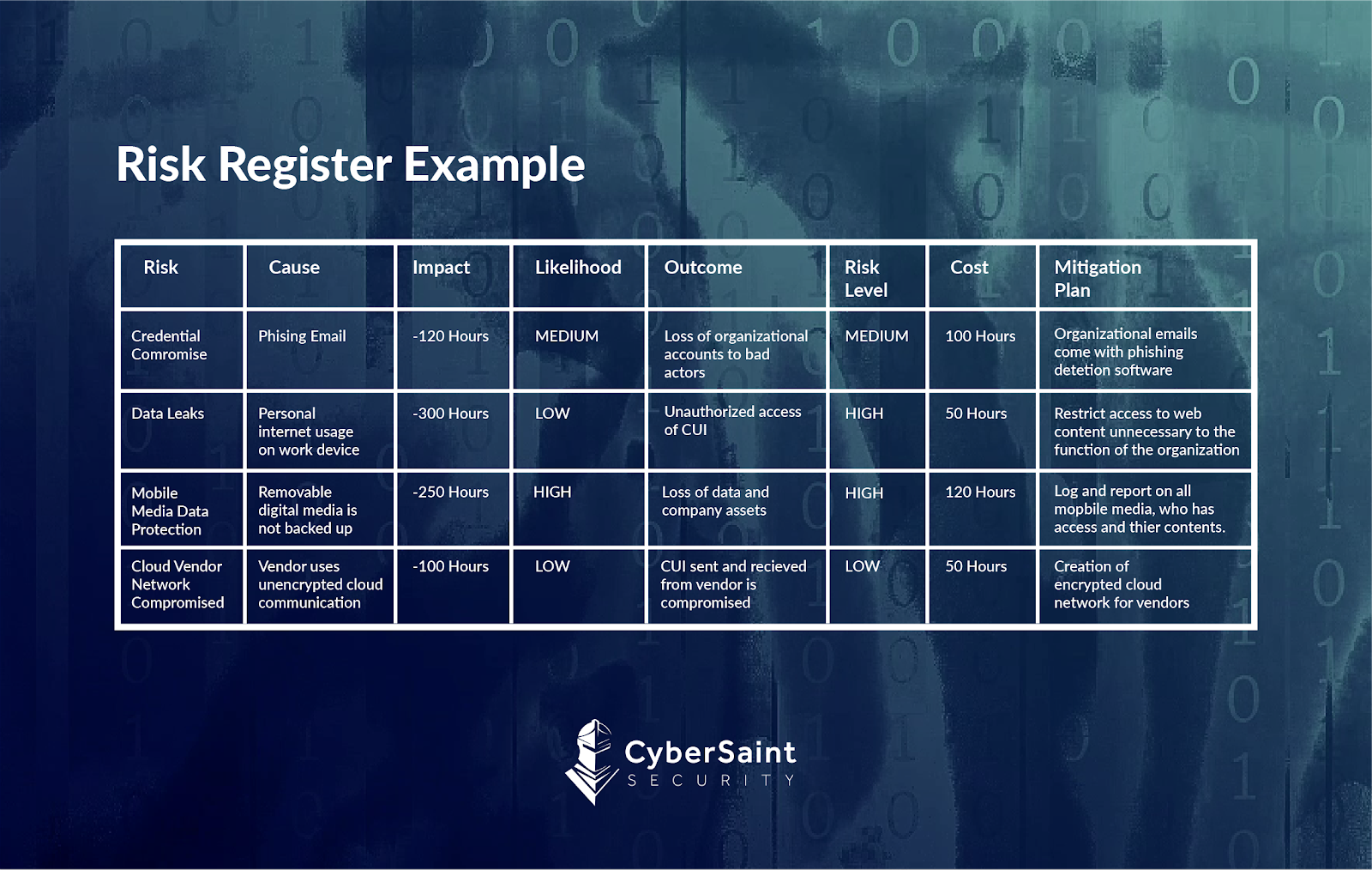
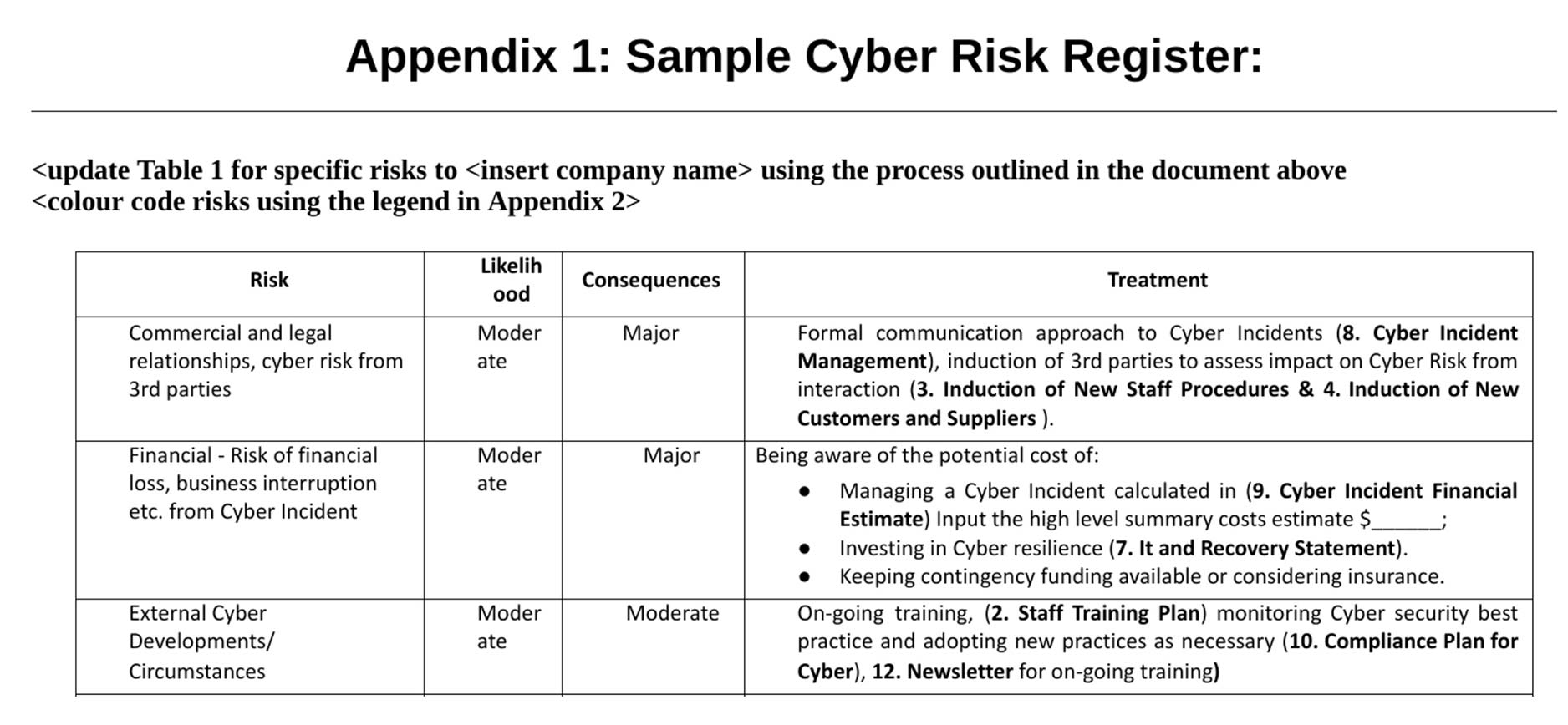
Cybersecurity Risk Register Template - Web to conduct a cybersecurity risk assessment, we recommend following these five steps. Web a risk register is a key element to provide your management team with a bigger picture of your exposure to risks and help them understand each of them. Approaches, methodologies, implementation guides, mappings to the framework, case studies, educational materials,. How can risk join help? Cybersecurity ris k register (csrr); Web documenting the likelihood and impact of various threat events through cybersecurity risk registers integrated into an enterprise risk profile helps to later. Linking controls to “best practice”. You can download our free risk register template for excel. Getapp has the tools you need to stay ahead of the competition. Web students will be provided templates, tools, and checklists for performing a cybersecurity risk assessment and taught the skills necessary to use those resources effectively. How can risk join help? Web risk register definition (s): Web a cyber risk register template is an essential tool for any organization that wants to effectively manage and mitigate cyber risks. The case for using multiple risk registers. Similar processes, and the general use of risk registers, are helpful to. A central record of current risks, and related information, for a given scope or organization. Web cybersecurity risk assessment templates let’s take a look at the cis critical security controls, the national institute of standards and technology (nist). Linking controls to “best practice”. Similar processes, and the general use of risk registers, are helpful to. Current risks are comprised of. Web crafting a risk register ‘power tool’ as the base for a multiyear cybersecurity plan; Web a risk register is a key element to provide your management team with a bigger picture of your exposure to risks and help them understand each of them. Web overview more than ever, organizations must balance a rapidly evolving cybersecurity and privacy threat landscape. Managing enterprise cybersecurity risk and its related a&a procedural guides. Approaches, methodologies, implementation guides, mappings to the framework, case studies, educational materials,. Web risk information, such as through cybersecurity risk registers (csrrs) and risk detail records (rdrs). Web resources include, but are not limited to: Web students will be provided templates, tools, and checklists for performing a cybersecurity risk assessment. A central record of current risks, and related information, for a given scope or organization. Web the pram is a tool that applies the risk model from nistir 8062 and helps organizations analyze, assess, and prioritize privacy risks to determine how to respond. Web to conduct a cybersecurity risk assessment, we recommend following these five steps. Web a cyber risk. Web a risk register is a key element to provide your management team with a bigger picture of your exposure to risks and help them understand each of them. How can risk join help? Evaluate the scope for the risk assessment. You can download our free risk register template for excel. Web the pram is a tool that applies the. Web a cyber risk register template is an essential tool for any organization that wants to effectively manage and mitigate cyber risks. Web the pram is a tool that applies the risk model from nistir 8062 and helps organizations analyze, assess, and prioritize privacy risks to determine how to respond. Web to conduct a cybersecurity risk assessment, we recommend following. Linking controls to “best practice”. The first step in conducting a. The case for using multiple risk registers. Web cybersecurity risk management (csrm); Web a risk register is a key element to provide your management team with a bigger picture of your exposure to risks and help them understand each of them. Web a cyber risk register template is an essential tool for any organization that wants to effectively manage and mitigate cyber risks. Similar processes, and the general use of risk registers, are helpful to. Web a risk register is a key element to provide your management team with a bigger picture of your exposure to risks and help them understand. Evaluate the scope for the risk assessment. Web cybersecurity risk management (csrm); Linking controls to “best practice”. Approaches, methodologies, implementation guides, mappings to the framework, case studies, educational materials,. Web risk information, such as through cybersecurity risk registers (csrrs) and risk detail records (rdrs). In hyperproof, organizations can set up multiple risk registers to track different types of risks and customize the scales/risk scoring for each risk register. It’s a starting point for building out your own risk register. Web students will be provided templates, tools, and checklists for performing a cybersecurity risk assessment and taught the skills necessary to use those resources effectively. Linking controls to “best practice”. The case for using multiple risk registers. Web august 21, 2023. Web crafting a risk register ‘power tool’ as the base for a multiyear cybersecurity plan; Web overview more than ever, organizations must balance a rapidly evolving cybersecurity and privacy threat landscape against the need to fulfill business requirements on an. The michigan department of technology, management & budget’s client service center (csc) serves as the primary point of contact for state of. Web the pram is a tool that applies the risk model from nistir 8062 and helps organizations analyze, assess, and prioritize privacy risks to determine how to respond. Evaluate the scope for the risk assessment. Web to conduct a cybersecurity risk assessment, we recommend following these five steps. Web documenting the likelihood and impact of various threat events through cybersecurity risk registers integrated into an enterprise risk profile helps to later. Web risk register definition (s): Getapp has the tools you need to stay ahead of the competition. Web of leaders cannot see the full spectrum of online threats against their businesses. Current risks are comprised of both accepted risks and risk. Web cybersecurity risk management (csrm); Managing enterprise cybersecurity risk and its related a&a procedural guides. Cybersecurity ris k register (csrr); Web to conduct a cybersecurity risk assessment, we recommend following these five steps. Web cybersecurity risk assessment templates let’s take a look at the cis critical security controls, the national institute of standards and technology (nist). Evaluate the scope for the risk assessment. Web students will be provided templates, tools, and checklists for performing a cybersecurity risk assessment and taught the skills necessary to use those resources effectively. You can download our free risk register template for excel. Managing enterprise cybersecurity risk and its related a&a procedural guides. Getapp has the tools you need to stay ahead of the competition. The case for using multiple risk registers. Linking controls to “best practice”. Web the pram is a tool that applies the risk model from nistir 8062 and helps organizations analyze, assess, and prioritize privacy risks to determine how to respond. Current risks are comprised of both accepted risks and risk. Approaches, methodologies, implementation guides, mappings to the framework, case studies, educational materials,. Web cybersecurity risk management (csrm); Web of leaders cannot see the full spectrum of online threats against their businesses. How can risk join help? It’s a starting point for building out your own risk register.48 Cyber Security Powerpoint Template Free Heritagechristiancollege
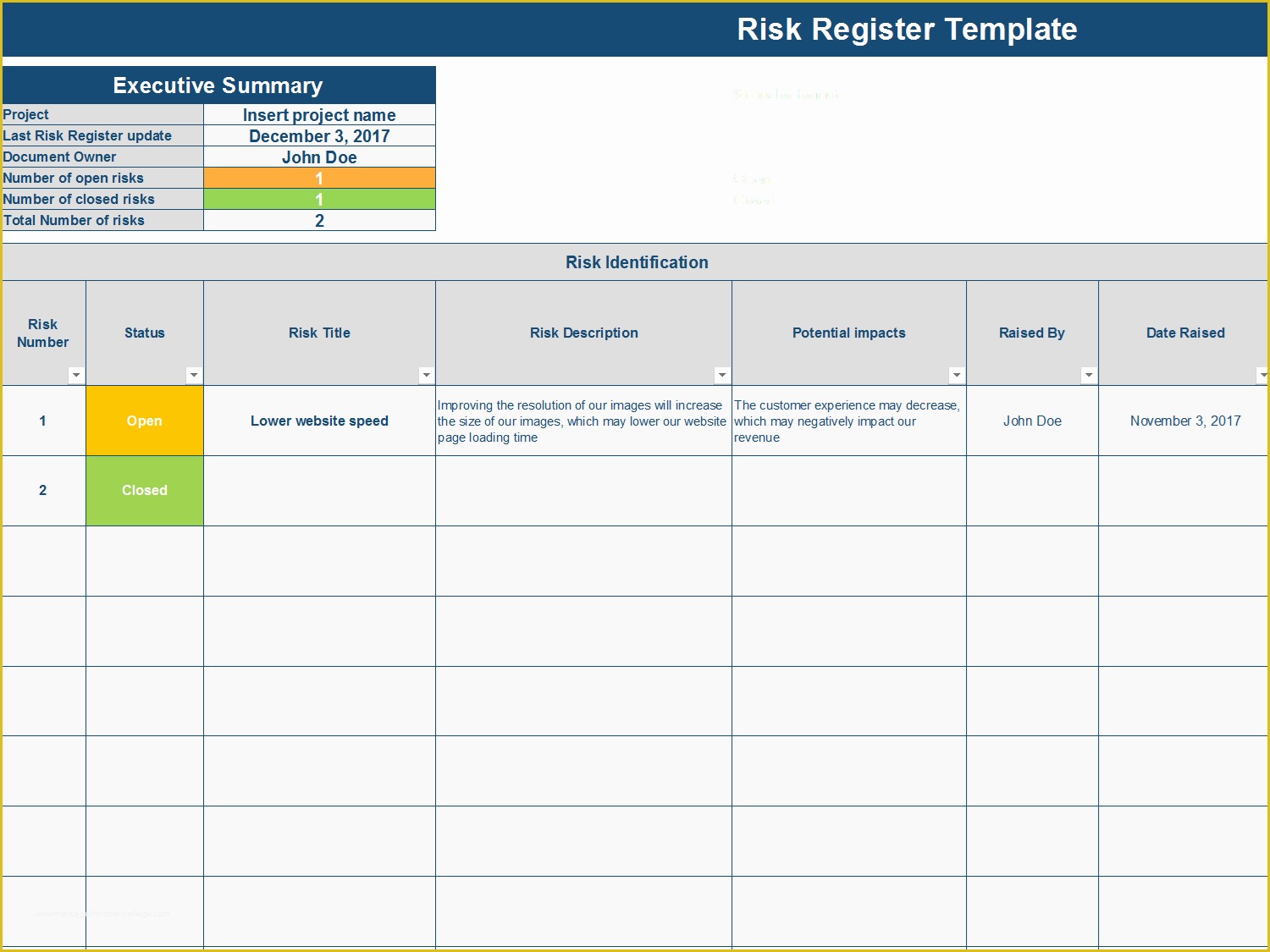
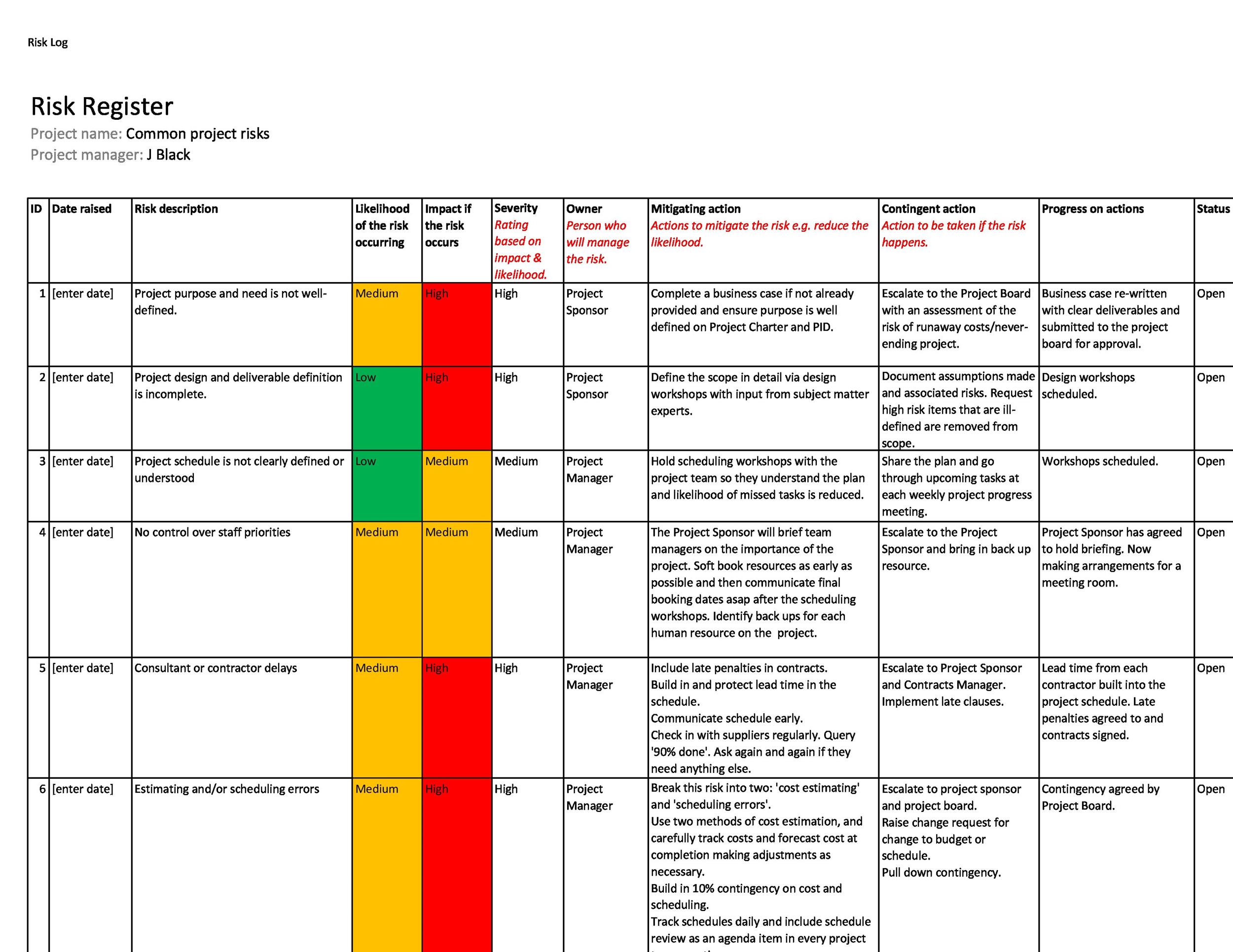
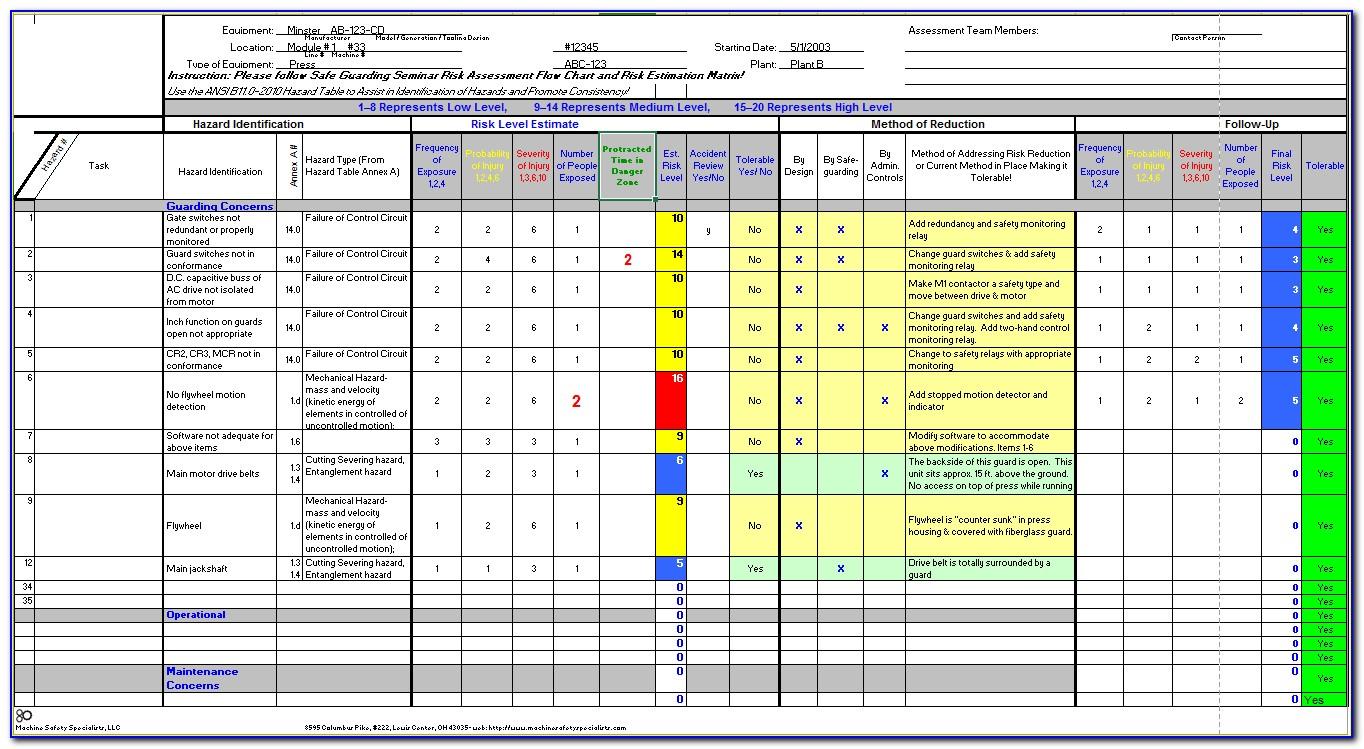
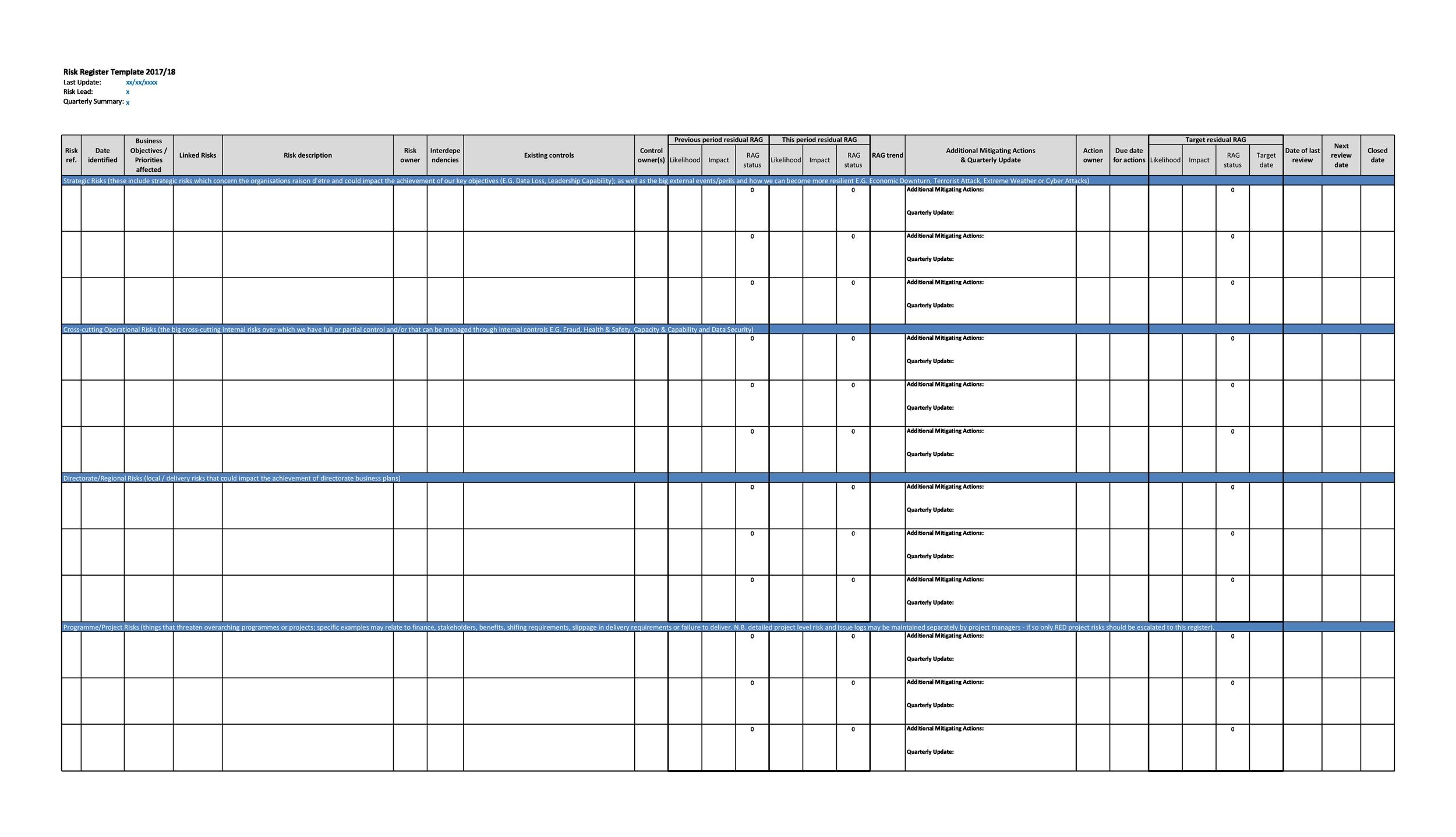
45 Useful Risk Register Templates (Word & Excel) ᐅ TemplateLab
Cybersecurity Risk Assessment Chart For Organization Presentation
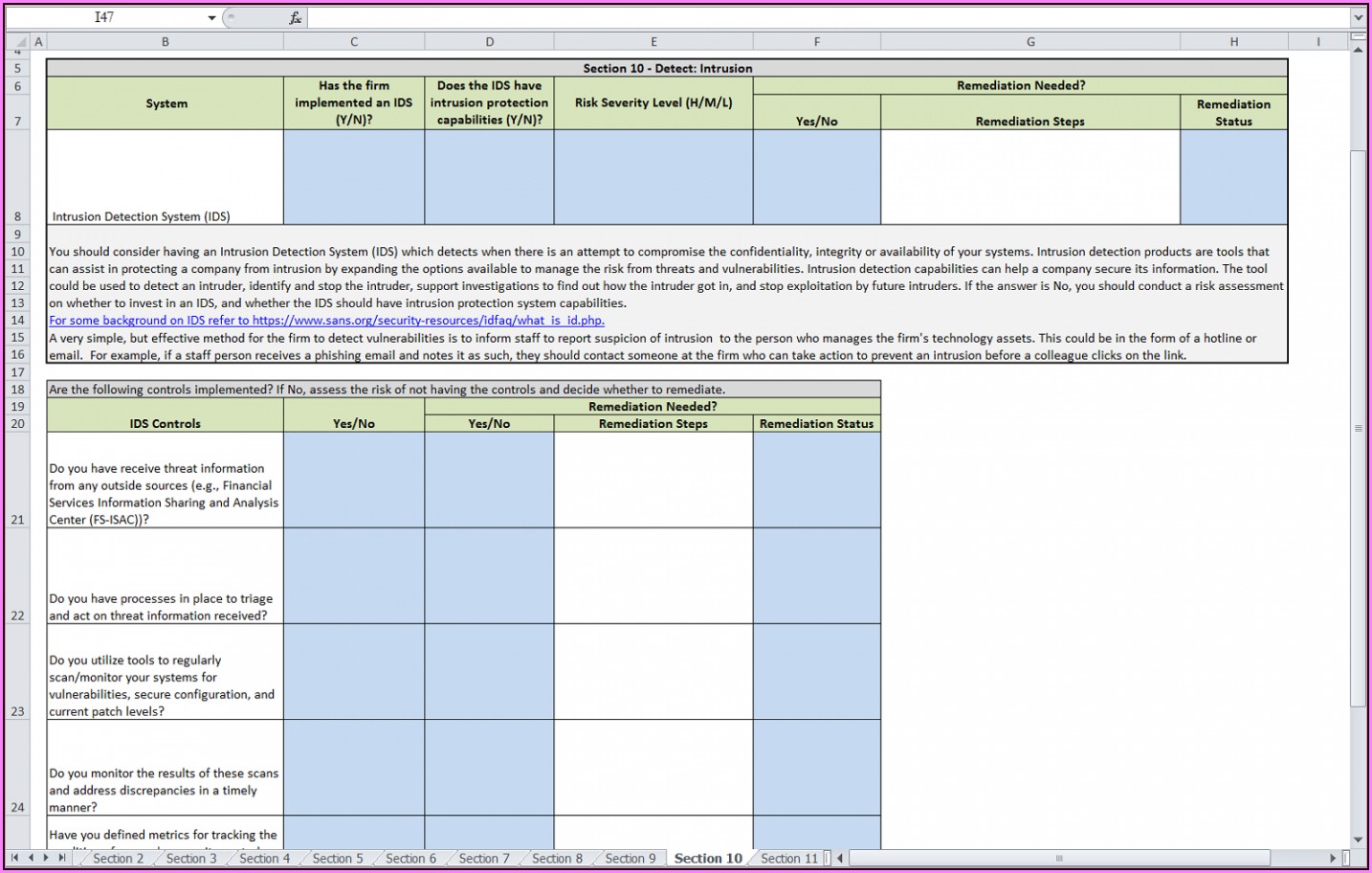
Cybersecurity Risk Assessment Template for creating cybersecurity
Nist 800 Risk Assessment Template / of the national
Risk Register Examples for Cybersecurity Leaders Security Boulevard
Risk Assessment Risk Register Template Excel Construction Risk
Cyber Crime Risk Assessment Adam M. Erickson
Cyber Security Assessment Report Template Template 1 Resume
Cyber Procedures to Tailor and Implement Pink Cyber Cyber security
Web Overview More Than Ever, Organizations Must Balance A Rapidly Evolving Cybersecurity And Privacy Threat Landscape Against The Need To Fulfill Business Requirements On An.
The Michigan Department Of Technology, Management & Budget’s Client Service Center (Csc) Serves As The Primary Point Of Contact For State Of.
Similar Processes, And The General Use Of Risk Registers, Are Helpful To.
Web Resources Include, But Are Not Limited To:
Related Post: